Information Security (InfoSec) Compliance Ensure Compliance With InfoSec Policy and Regulations
Identify Risks and Monitor Cyber Security
Automatically identify InfoSec risks and move from one-time or annual risk reviews to continuous monitoring of supplier cyber security risk.
Protect Sensitive Information
Prevent theft of sensitive information across your organization's supply chain.
Document and Report Risks & Remediation
Document control effectiveness while automating tracking and reporting of risks and risk remediation with confidence.
Identify Risks & Monitor Cyber Security
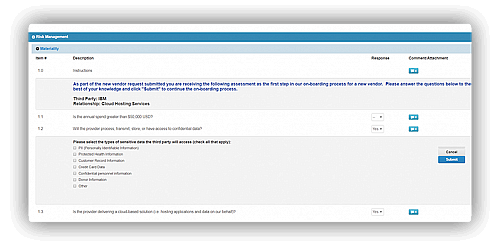
Automatically Identify InfoSec Risks
Coupa's information security risk assessment solution helps efficiently identify third-party access to sensitive information which opens the door to InfoSec risk, and scope the appropriate controls for each relationship all through a digital process.
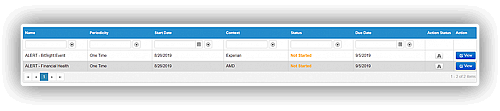
Continuously Monitor Cyber Security
Get rid of extensive manual questionnaires to ensure compliance with cybersecurity controls. Move from one-time or annual risk reviews to continuous monitoring of supplier cyber security risk by integrating data from providers such as BitSight or Risk Recon and raising alerts for review.
Protect Sensitive Information
Prevent Theft of Sensitive Information
Comprehensively identify the third-party relationships that represent inherent InfoSec risk, put plans in place to mitigate that risk, and monitor your third parties as they demonstrate their safeguards to protect your critical private information.

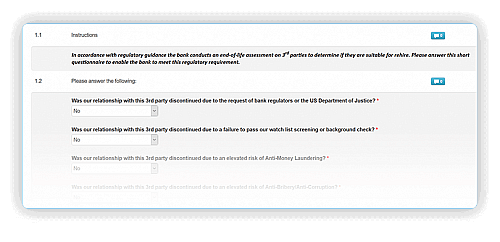
Drive Off-Boarding Compliance
Ensure compliance with contractual terms for off-boarding—such return of sensitive data—while streamlining termination and transition and maintaining auditable records.
Document & Report Risks & Remediation
Document Control Effectiveness
Automatically map questionnaire data to specific controls for faster and easier assessment. Automate document control effectiveness for completed assessments to satisfy internal and external regulatory review.
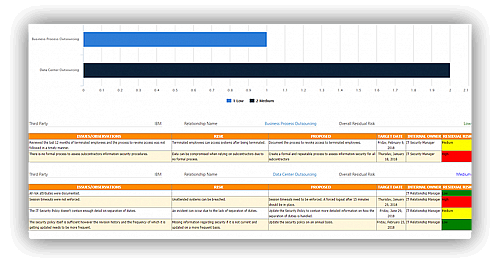
Report Risks & Remediation With Confidence
Automate tracking and reporting of risks and risk remediation with a Risk Register, Vendor Action Plan, Assessment Summary, and Failed Controls reports.


