The 3 Most Critical Areas That Prevent Treasury Management Fraud

Has the moment finally come when corporate treasurers and cash managers can spend a little less time on fraud prevention? After all, a 2022 AFP report found that not only has payment fraud activity been declining since 2018, organizations observed that remote work did not play a significant role in instances of payment fraud during 2021. Does this mean that treasury management professionals can pivot to other business priorities?
Clearly, the answer is no. Looming recessions can increase the risk of fraud, putting corporate treasurers and cash managers in a tough spot. Layoffs, for example, often wreak havoc on internal control systems. Increased financial pressure may drive some employees to take desperate and unethical measures to stay within budget.
Fraud prevention is a challenge that corporate treasurers and cash managers know they must address. There are more tools at their disposal than ever before to prevent fraud — starting with addressing the systems, processes, and people involved in their organization. Let’s take a closer look at these critical areas.
1. Systems
Just because an organization has a treasury management system (TMS) doesn’t automatically make fraud prevention airtight. As a first step, it’s important to understand two things: the central and decentral workflows in place to process payments, and the system landscape within the organization. Consider:
- What systems do you have, and which workflows do you follow? (For example: Is there one system to process payments and another to manage liquidity? Can certain workflows be interrupted or stopped?)
- Do you have full visibility into all transactions across the business? (Corporate treasurers and cash managers must know what’s coming in as well as what’s going out.)
- What measures do you currently take to prevent fraud? (These can be process-related, such as segregation of duties, or more technical in nature, such as multi-level authentication and IP restrictions.)
Using one system centrally with various other tools locally makes it difficult to establish and enforce reliable group-wide control. When local entities and bank accounts aren’t managed in a TMS, market data, account statements, and deal transcripts are vulnerable to manipulation. A disconnected system (or no system at all) also allows bad actors to open a bank account and make payments unnoticed since the head office doesn’t know about the account and can’t put any controls in place. Processes may be centralized or decentralized to suit a company’s operating model, but centralized transparency is crucial.
Our experience at Coupa Treasury also shows that a small percentage of the company — the local entities — usually makes up a large percentage of the fraud risk. This is because hackers and other perpetrators are much more likely to target a company’s local entities, not HQ.
Meanwhile, a limited overview of cash flow makes it difficult to detect irregularities or weak points across the organization. An integrated Business Spend Management (BSM) platform where real-time payments data related to accounts payable activity helps corporate treasurers and cash managers gain visibility into spend patterns. And most importantly, a system without proper multi-level authentication — such as rigorous access controls like SSO coupled with IP restrictions and token log-in — creates vulnerabilities. In essence, corporate treasury departments can’t ensure processes are low-risk if the system is not up to par.
Get Your Copy Now
2. Processes
The term “process” covers a lot of ground in treasury management. Generally speaking, treasury management processes fall into three broad categories. Security plays a major role in each:
- Payment file creation: Where does the file originate? Who was involved in creating and sending it? How do employees review and verify supplier information?
- Payment and payment file approval: Who approves these files and payments? Which employees have which approval rights? Does everyone follow the minimum of a four-eyes principle?
- Payment path from the organization’s treasury department to the bank: What security barriers are in place? Which employees can “touch” a payment in terms of bank mandates and signature rights?
Processes can only be secure if they’ve been designed to be transparent. Segregation of duties (SOD) is a setup that makes it impossible for an employee to be in a position to both commit and conceal fraud and mistakes. Most companies with treasury departments have followed this approach. It stipulates that both the Head of Treasury and a separate administrator, such as someone in HR or IT, approve new users in the system before they can access the TMS — regardless of the specific modules those users will actually work with, such as cash visibility, payments, foreign exchange, and debt.
A group-wide platform also helps create and enforce transparency. It empowers corporate treasurers and cash managers to standardize processes and puts systemic control mechanisms in place to prevent fraud from happening across all bank access points. Measures including dynamic allow lists, leveraging AI and community data, and strict governance are faster, more effective, and less expensive than random, manual inspections that may happen after fraud has occurred.
Dynamic allow lists
As an organization grows, its banking and supplier landscapes grow more complex. Activities that were once manageable through manual work become incredibly time-consuming and prone to error. Some examples: verifying a supplier’s remit-to information; ensuring no fake beneficiaries have been added to the master data; stopping payments to regions under sanctions. Dynamic allow lists powered by AI can genuinely transform how a growing company prevents fraud.
Allow lists work by guiding a system to process only payments to verified beneficiaries on the list. Any other payments require additional verification. Companies can create allow lists by compiling all bank account connections classified as trustworthy across the group and then use that information as a filter. The best allow lists are dynamic — that is, they go beyond filtering. Additional screening mechanisms built into the system can, for example, cross-reference payments against sanction and embargo lists before alerting users to a potentially illegal payment.
AI and community data
AI delivers powerful fraud detection within a TMS. It screens payments proactively, in amounts and at speeds that manual processes simply can’t match. Coupa’s proprietary AI also identifies transactions that don’t seem suspicious individually, but indicate non-compliant behavior when reviewed together.
This AI also underpins Coupa’s unique Community.ai, a suite of innovations that aggregates, anonymizes, and analyzes transaction data generated by more than 3,000 customers and $4 trillion in cumulative spend flowing across the platform. Thanks to community data, corporate treasurers and cash managers can get visibility into vendor ratings, for example, determine if a supplier is at risk, or surface mismatched and potentially fraudulent payment information.
Strict governance
Banks and companies can certainly work together to reduce and prevent fraud, but companies must take the lead. There are two reasons for this. First, while banks do perform certain scans on payments, it is the company, and not the bank, that loses money through fraud. Banks also rely on bank mandates. If a payment comes through and the mandate is correct, the bank will execute on it - because bank employees can’t verify if the person on the mandate is still with the company.
Strict, transparent governance is essential, and it should address both approval processes and bank mandates.
At the bare minimum, payment approvals should:
- Set up SOD (see above) to prevent the riskiest practices, such as employees entering single payments on their own
- Enforce the use of templates to prevent employees from mistyping or altering international bank account numbers (IBANs)
- Define which employees can perform which actions, such as only entering payments, entering and approving payments, and entering or changing payment instructions templates
- Establish limits for payment approvals and signature rights (such as assigning rights at the bank account level; defining limits for people, for accounts, for currencies; and creating different levels of signatures on the bank mandate)
A system, like Coupa Treasury, improves security by generating additional dual approval chains down the line. This includes measures like multiple access levels limiting user signature rights and payment limits. Take it a step further with token log-ins and two-step authentication when employees seek to enter payment information.
Companies can also proactively manage bank mandates to reduce fraud risk. Treasury departments should ensure that:
- An employee’s bank mandates are immediately shut off when that person leaves the company
- Signature rights are clearly assigned within the mandate, such as adding a new bank account, changing the type of bank account, and adding bank services
Watch an On-Demand Demo Now
3. People
At the end of the day, fraud is perpetrated by people — and more often than that, by people working inside the company itself. Just like the plot of “Office Space,” a man used malicious code to send small increments of money from his employer to his personal account. In total, he managed to transfer $300,000 before getting caught. It’s an example of why employees should be a priority in preventing fraud in your organization, especially when it comes to asset misappropriation. And while cases like the one mentioned above require intentional action on an employee’s part, others rely on the gullibility of individual employees such as the increasingly popular business email compromise (BEC) scam.
Deterring Asset Misappropriation
Internal employee fraud shows up most often as asset misappropriation, accounting for 86% of fraud cases globally in 2022, according to a report by the Association of Certified Fraud Examiners (ACFE). Common tactics include false billing schemes, nabbing inventory, stealing payments in transit, and altering checks.
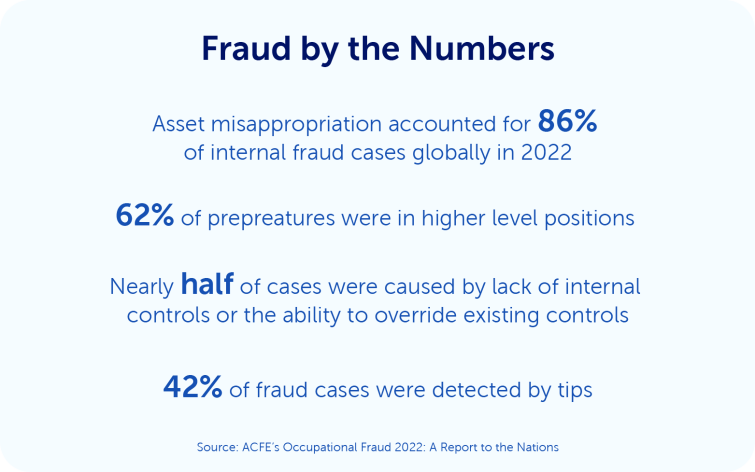
What kinds of employees are most likely to partake in fraud schemes? Most are in roles of higher levels of authority, which may come as a surprise. What gives them the ability to steal? Nearly half of the employee-related fraud cases are due to a lack of internal controls or the ability to override internal controls. Ensuring payment processes are protected, with measures such as allow lists, AI, and strict governance, is the best way to curb fraud, even from high-level employees. With more eyes reviewing payments at all levels, treasury departments can reduce the chances of asset misappropriation.
Taking into account that 42% of fraud cases were detected by tip-offs from employees, customers, vendors, and anonymous reporters — nearly three times as many cases as the next popular method — means combining a strong payment process with a fraud hotline could better help protect an organization from internal fraud.
Preventing business email compromise (BEC) scams
As companies moved operations online during the start of the pandemic, fraudsters took the opportunity to ramp up BEC scams. It involves the hacking or spoofing of a business or personal email account and sending emails to employees with a request for a wire payment.
Phishing attacks, which include BEC scams, are the fastest-growing fraud types around the world, according to the FBI. They’re also getting more sophisticated. Fraudsters are now using virtual meetings to trick employees. After they’ve successfully compromised a CEO’s or CFO’s email, they’ll invite an employee to a virtual meeting to initiate the wire transfer. Using a still photo of the compromised business executive, the fraudster may claim their audio isn’t working or they’ll use “deep fake” audio. These tricks seem to work. In 2021, BEC and email account compromise (EAC) scams accounted for over $2 billion in losses for businesses worldwide.
What can corporate treasury departments do to prevent them?
- Raise awareness. Many employees may be unaware of the alarming number of cyberattacks attempted on them every day. Hold regular training sessions or send out quarterly newsletters to educate them on emerging trends, the characteristics of certain scams, and personal measures they can take to protect themselves.
- Use phishing simulators. One of the best ways to learn how to avoid a scam is to experience one first-hand. A phishing simulator sends out company-controlled phishing attempts to employees and analyzes their responses. The tool helps employees develop the skills necessary to detect these kinds of scams.
- Protect payment processes. Ensuring there is a SOD for payment processes is the best way to prevent these kinds of scams from happening at all. Even if an employee unknowingly attempts to send a fraudulent payment, the requirement of a separate approval lessens the chance of that payment ever being posted. SOD can be as streamlined as the four-eyes principle, but it can also be differentiated to include more people or different groups of people when higher-value payments are involved.
Putting structural and automated security measures in place along with raising awareness among employees makes businesses less susceptible to emerging fraud schemes.
Corporate treasurers and cash managers need the right tools to stay ahead of fraud
Turbulent economic times can increase the risk of fraud. It’s more important than ever for treasury departments to review the system, processes, and people at their organizations, from HQ to the smallest entity. Coupa Treasury helps safeguard all three areas while reducing costs. That’s how Bilfinger, a civil and industrial construction company, saved 15% in banking fees and increased transparency and security in their process by 100%.
Get Your Copy Now